Technology
Crucial Insights: Essential Aspects of Cybersecurity for Today’s Digital World

In today’s highly connected digital landscape, cybersecurity has become crucial for protecting individuals, organizations, and infrastructure. As cyber threats continue to evolve rapidly, gaining crucial insights into the essential aspects of cybersecurity is vital.
Having strong cybersecurity measures in place is thus an essential aspect of protecting these critical assets. Adopting defense-in-depth cybersecurity protocols enables businesses to detect and thwart the vast majority of common cyberattacks as well as more sophisticated threats.
With proper implementation guided by robust frameworks like NIST, companies can safeguard their systems while contributing to the strengthened security posture of our increasingly digital-focused society. Referring frequently to trustworthy cybersecurity guides can assist all types of public and private entities in upholding reliable data protection.
The Ever-Growing Threat Landscape
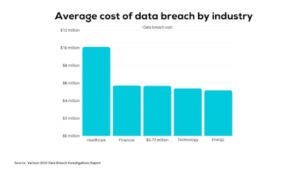
With cyberattacks estimated to cost the global economy over $6 trillion annually by 2021, it’s clear that the threat landscape is expanding. In 2021 alone, ransomware attacks grew by a staggering 600%, inflicting tremendous damage (CISA, 2022). These threats exploit vulnerabilities across networks, endpoints, and applications. Without proactive cybersecurity, entities risk disruption, fraud, and irreparable reputational harm.
In this comprehensive cybersecurity guide, some of the key defensive strategies that organizations should implement are included. They are:
- Keeping all software patched and updated
- Using multi-factor authentication
- Establishing strict access controls and permissions
- Securing endpoints like company devices and servers
- Developing cyber incident response plans
- Training employees on security best practices, and
- Investing in powerful tools like AI-enhanced firewalls and malware detection.
Core Aspects of Effective Cybersecurity
Given the risks, understanding the fundamental aspects of cybersecurity is key for security teams. First, robust network security controls like firewalls, intrusion prevention, and threat intelligence protect infrastructure. Endpoint security solutions safeguard devices, servers, and users.
With 95% of breaches caused by human error, authentication systems that validate user identities are essential. Encrypting sensitive data limits unauthorized access when stolen. Maintaining an incident response plan enables rapid containment of attacks – but only 25% of organizations are prepared. Training staff and performing exercises regularly are also vital.
Harnessing Emerging Technologies
Advanced technologies like artificial intelligence (AI) and blockchain provide immense opportunities to enhance cybersecurity. AI-driven systems can slash response times to cyberattacks from hours to just seconds by identifying threats instantly (IBM, 2022). The immutable ledger capabilities of blockchain make it arguably the most secure way to store and share sensitive data.
Leveraging automation, machine learning, and other innovations allow security teams to be proactive. Emerging tech also aids with tasks like penetration testing, compliance audits, and access management.
Navigating the Regulatory Environment
Organizations must also comply with relevant cybersecurity regulations and frameworks. In the EU, the General Data Protection Regulation (GDPR) mandates data security controls. The Health Insurance Portability and Accountability Act (HIPAA) regulates the protection of medical information. Adhering to ISO 27001 standards demonstrates a commitment to best practices.
Staying updated on evolving regulations is crucial. Building compliance into system designs and processes proactively enhances posture while enabling operational agility.
Organizations must comply with relevant cybersecurity regulations and frameworks that apply to their industry and jurisdiction. Some key regulations include:
General Data Protection Regulation (GDPR): This EU regulation mandates data protection and privacy controls for organizations handling data of EU citizens. Key requirements include data encryption, breach notification within 72 hours, and privacy by design.
Health Insurance Portability and Accountability Act (HIPAA): HIPAA establishes data privacy and security requirements for healthcare providers, payers, and business associates in the US. It regulates protected health information (PHI). Controls like access management, transmission security, and audit logs are required.
ISO/IEC 27001: This international standard outlines requirements for an information security management system (ISMS). It provides a risk-based framework for managing sensitive data through best practices like risk assessments, access control, and encryption. Organizations can achieve ISO 27001 certification.
NIST Cybersecurity Framework: Developed by the US National Institute of Standards and Technology (NIST), this framework provides industry standards and best practices for cybersecurity policies and risk management. It is aligned to ISO 27001.
NERC CIP: The North American Electric Reliability Corporation’s Critical Infrastructure Protection (NERC CIP) standards regulate cybersecurity for power grid assets. They mandate controls like network segregation, vulnerability management, and change management.
Staying updated on new and evolving regulations is crucial for compliance. Building compliance controls into system architectures and processes from the start enables organizations to maintain security, privacy, and resilience while supporting operations.
Best Practices for Individuals and Organizations
Recommended cybersecurity best practices include strong password hygiene, multi-factor authentication, timely patching, and employee education. Avoiding risky links and files, encrypting drives, and enabling automatic updates all help.
For organizations, regular vulnerability assessments, secure system configurations, and third-party risk management are key. Developing a cybersecurity-focused workplace culture is also imperative.
Recommended Cybersecurity Best Practices for Individuals:
- Use strong, unique passwords and enable multi-factor authentication (MFA) wherever possible. Avoid reusing passwords.
- Be vigilant of phishing attempts. Avoid clicking suspicious links or opening unverified attachments and files.
- Keep all systems and software up-to-date by enabling automatic updates. Patch security vulnerabilities promptly.
- Use a password manager app to securely generate and store login credentials.
- Encrypt hard drives and backup data regularly on external storage devices.
Essential Cybersecurity Best Practices for Organizations:
- Perform regular risk assessments to identify vulnerabilities in systems, processes, and business environments.
- Implement robust identity and access management controls, such as MFA, single sign-on (SSO), and privileged access management (PAM).
- Provide ongoing cybersecurity awareness training to employees to create a security-focused organizational culture.
- Maintain and regularly test incident response plans to enable rapid containment and recovery from security events.
- Deploy data loss prevention (DLP) systems to secure sensitive information and prevent unauthorized access or exfiltration.
- Perform periodic penetration testing and red team exercises to assess the effectiveness of security controls. Remediate gaps identified.
Adopting these fundamental individual and organizational best practices provides a strong foundation for enhancing cyber resilience against evolving threats.
FAQs
- What’s the primary difference between cybersecurity and information security?
Cybersecurity focuses on protecting systems, networks, and data from digital attacks. Information security safeguards the confidentiality, integrity, and availability of all data assets.
- How can small businesses strengthen cybersecurity on a budget?
Low-cost methods like training staff, using cloud services selectively, and leveraging free toolkits from agencies like NIST and CISA can significantly improve posture.
- What are the key challenges in securing IoT devices?
Vulnerabilities in IoT devices themselves, lack of visibility over expansive ecosystems, and difficulties patching at scale all pose major challenges.
Conclusion
As digital transformation accelerates globally, prioritizing cybersecurity and gaining crucial insights have become indispensable. Awareness of essential aspects like network security, emerging tech adoption, regulatory alignment, and best practices enable resilient protection in the face of evolving threats. Cybersecurity necessitates continuous learning, adaptation, and proactive measures.
Technology
LeiaPix Converter: Easy 2D to 3D Conversion

Introduction
In a world where digital visuals are paramount, enhancing your images can make a significant difference. Whether you’re a photographer, digital artist, or marketer, LeiaPix Converter offers an exciting way to turn your flat, 2D images into engaging 3D visuals. Let’s dive into how this innovative tool can transform your creative projects.
What is LeiaPix Converter?
Definition and Purpose
LeiaPix Converter is a groundbreaking web application designed to convert traditional 2D photos into mesmerizing 3D images. By leveraging advanced AI technology, LeiaPix Converter generates depth maps that bring a new dimension to your visuals. This tool is perfect for anyone looking to add depth and dynamism to their images without requiring extensive 3D modeling expertise.

How It Works
LeiaPix Converter uses sophisticated algorithms to analyze the depth and contours of your 2D images. It then creates a depth map, which translates the flat image into a three-dimensional space. This process adds layers of depth, making your photos look more immersive and engaging.
Key Features of LeiaPix Converter
AI Technology
The heart of LeiaPix Converter lies in its use of artificial intelligence. The AI algorithms meticulously scan your images to create accurate depth maps, ensuring that the 3D effect is realistic and captivating.
Depth Map Generation
Depth maps are essential for creating 3D effects. LeiaPix Converter’s advanced depth map generation transforms ordinary images into dynamic 3D visuals by analyzing various depth levels within the image.
User-Friendly Interface
LeiaPix Converter boasts a clean and intuitive interface, making it accessible for both beginners and experienced users. With simple controls and straightforward steps, converting your images to 3D has never been easier.
Benefits of Using LeiaPix Converter
Enhanced Visual Appeal
One of the primary benefits of using LeiaPix Converter is the enhanced visual appeal of your images. The added depth and dimension make your visuals stand out, whether you’re showcasing artwork or promoting a product.
No Need for Advanced 3D Skills
Unlike traditional 3D modeling software, LeiaPix Converter doesn’t require advanced 3D skills. Its AI-driven process simplifies the conversion, allowing you to achieve impressive 3D effects without a steep learning curve.
Free Accessibility
LeiaPix Converter is available for free, making it an excellent tool for users on a budget. You can enjoy the full range of features without any cost, making it a valuable resource for digital creators of all kinds.
How to Use LeiaPix Converter
Step-by-Step Guide
Using LeiaPix Converter is straightforward. Here’s a step-by-step guide to help you get started:
- Upload Your Image: Start by uploading the 2D image you want to convert. LeiaPix Converter supports various file formats, including JPEG and PNG.
- Adjust Settings: Customize the depth settings to your liking. You can adjust parameters such as depth intensity and 3D effect strength to fine-tune the result.
- Download Your 3D Image: Once you’re satisfied with the adjustments, click the “Convert” button. After processing, download your newly created 3D image.
Uploading Your Image
Ensure your image is of high quality for the best results. The clearer the image, the more accurate the depth map will be, leading to a more impressive 3D effect.
Adjusting Settings
Experiment with different settings to find the perfect balance. You can tweak depth levels, shadows, and highlights to match your creative vision.
Downloading Your 3D Image
After conversion, download the 3D image to your device. You can now use it for various applications, from digital art to marketing materials.
Applications of 3D Images
Digital Art
Artists can use LeiaPix Converter to add a new dimension to their work. The 3D effects can make digital art pieces more engaging and visually striking.
Photography
Photographers can enhance their portfolios by turning 2D photos into 3D images. This added depth can make images more captivating and memorable.
Marketing and Social Media
In marketing and social media, eye-catching visuals are crucial. 3D images can draw more attention and increase engagement with your content.
Comparing LeiaPix Converter to Other Tools
LeiaPix vs. Traditional 3D Software
Traditional 3D software often requires extensive training and expertise. In contrast, LeiaPix Converter simplifies the process with its AI-driven approach, making 3D conversion accessible to everyone.
LeiaPix vs. Other AI 3D Converters
While there are other AI-powered 3D converters, LeiaPix stands out for its ease of use and effectiveness. Its depth map generation ensures high-quality 3D results with minimal effort.
Common Issues and Troubleshooting
Image Quality Problems
If your image quality isn’t up to par, ensure it’s high-resolution and clear. Low-quality images may produce subpar 3D effects.
Depth Map Errors
Occasionally, the depth map may not be perfect. Adjust the settings to improve accuracy or try uploading a different image.
Fixing Common Glitches
Restarting the tool or re-uploading the image can often resolve minor glitches. If problems persist, consult the LeiaPix support team for assistance.
Advanced Tips and Tricks
Optimizing Image Quality
For the best results, use high-resolution images. The more detail in your photo, the better the depth map and overall 3D effect.
Using LeiaPix Converter for Different Image Types
Experiment with various types of images, from portraits to landscapes. Each type may require different settings to achieve the best 3D effect.
Combining LeiaPix with Other Tools
You can enhance your 3D images further by combining LeiaPix with other editing tools. Use photo editors to fine-tune details and add finishing touches.
Case Studies and Success Stories
Examples of Stunning Transformations
Many users have achieved impressive results with LeiaPix Converter. From breathtaking digital art to captivating marketing visuals, the possibilities are endless.
User Experiences
User testimonials highlight how LeiaPix Converter has transformed their projects. Whether for personal or professional use, the feedback is overwhelmingly positive.
Conclusion
In summary, LeiaPix Converter is a powerful and accessible tool for transforming 2D images into dynamic 3D visuals. Its AI-driven technology simplifies the process, making it easy for anyone to enhance their images. Whether you’re a digital artist, photographer, or marketer, LeiaPix Converter offers a simple yet effective way to add depth and engagement to your visual content.
FAQs
What file formats does Lei’aPix Converter support?
LeiaPix Converter supports common file formats like JPEG and PNG.
Can Lei’aPix Converter handle high-resolution images?
Yes, Lei’aPix Converter can process high-resolution images to deliver detailed 3D effects.
Is Lei’aPix Converter free to use?
Yes, Lei’aPix Converter is available for free, offering all its features without any cost.
How long does it take to convert an image?
The conversion time depends on the image size and complexity, but it typically takes just a few minutes.
Are there any limitations on image size?
While there’s no strict size limit, very large images may take longer to process. For optimal results, use standard image sizes.
Technology
How Digital Art Ankinsart is Shaping the Future of Artistic Expression

Introduction
Digital art has revolutionized the way we think about creativity and expression. Among the numerous styles and techniques, Digital Art Ankinsart stands out as a leading force shaping the future of artistic expression. This innovative approach blends advanced technology with artistic vision, offering fresh perspectives and redefining traditional boundaries.
What is Digital Art Ankinsart?

Digital Art Ankinsart represents a modern evolution in the world of digital artistry. Rooted in the broader context of digital art, Ankinsart is characterized by its distinctive techniques and methodologies. It encompasses a wide range of styles, each unique in its approach but unified by the use of digital tools.
The Rise of Digital Art
The evolution of digital art can be traced back to the advent of computer technology. From rudimentary pixel art to sophisticated digital masterpieces, the journey has been marked by significant milestones. Technological advancements have played a crucial role, enabling artists to explore new realms of creativity.
Key Features of Ankinsart
Ankinsart is recognized for its unique features that set it apart from traditional digital art. Key aspects include:
- Unique Techniques: Ankinsart employs distinctive methods to create visually striking pieces.
- Tools and Software: Artists utilize advanced software and hardware to bring their visions to life.
How Ankinsart is Transforming Artistic Expression
Digital Art Ankinsart is transforming artistic expression by breaking away from conventional norms. It offers new possibilities, allowing artists to explore uncharted territories and push the boundaries of traditional art forms. This innovation fosters a fresh perspective on creativity and artistic exploration.
The Creative Process Behind Ankinsart
The creation of Ankinsart involves several stages:
- Conceptualization: Artists begin with brainstorming and sketching initial ideas.
- Execution and Refinement: Using digital tools, they bring their concepts to life, refining their work through various iterations.
Case Studies of Notable Ankinsart Works
To understand the impact of Ankinsart, let’s look at some notable examples:
- Example 1: This piece exemplifies Ankinsart’s ability to blend technology with artistry, resulting in a groundbreaking visual experience.
- Example 2: Another significant work that showcases innovations introduced by Ankinsart, influencing the digital art community.
The Role of Technology in Digital Art Ankinsart
Technology is at the heart of Ankinsart. Key elements include:
- Software and Hardware Integration: The seamless combination of digital tools enhances the creative process.
- Impact on Creativity: Advanced technology expands artistic possibilities and allows for greater experimentation.
Challenges and Criticisms of Digital Art
Despite its advancements, digital art faces challenges and criticisms:
- Common Criticisms: Some argue that digital art lacks the authenticity of traditional mediums.
- Overcoming Challenges: Artists continually adapt and innovate to address these critiques and advance the field.
Future Trends in Digital Art Ankinsart
The future of Digital Art Ankinsart is bright, with several trends emerging:
- Emerging Techniques: New methods and technologies will continue to evolve.
- Predictions: Expectations for the future include even more integration of technology and art.
Ankinsart in the Commercial World
Ankinsart is making significant strides in the commercial realm:
- Market Trends: The demand for digital art is growing, with Ankinsart leading the charge.
- Opportunities for Artists: There are increasing opportunities for artists to showcase and monetize their work.
The Influence of Ankinsart on Other Art Forms
Ankinsart’s influence extends beyond digital art:
- Cross-Medium Influences: It has inspired and collaborated with other art forms, creating a rich, interdisciplinary dialogue.
- Collaborative Projects: Joint ventures between Ankinsart and other artistic disciplines highlight its broad impact.
How to Get Started with Digital Art Ankinsart
For those interested in exploring Ankinsart:
- Tools and Resources: Various software and resources are available to help beginners get started.
- Learning and Development: Continuous learning and practice are key to mastering Ankinsart techniques.
Conclusion
Digital Art Ankinsart is not just a style but a movement that is reshaping artistic expression. By merging technology with creativity, it offers new opportunities and challenges traditional notions of art. As we look to the future, Ankinsart promises to be at the forefront of artistic innovation, continually pushing the boundaries of what is possible.
FAQs
What distinguishes Ankinsart from other digi’tal art styles?
Ankinsart is unique due to its specific techniques and integration of advanced digital tools, setting it apart from other digital art forms.
What are some popular tools used in Ankinsart?
Common tools include advanced graphic design software and high-performance tablets, which facilitate intricate and detailed artistic creation.
How has Ankinsart influenced traditional art forms?
Ankinsart has introduced new techniques and concepts that have inspired and blended with traditional art forms, leading to innovative cross-medium works.
What future trends should we expect in digital art?
Emerging trends include increased use of virtual and augmented reality, more interactive art experiences, and continued advancements in digital technology.
Where can I learn more about digi’tal art Ankinsart?
To learn more, explore online courses, tutorials, and forums dedicated to digi’tal art and Ankinsart. Many artists also share insights through their social media and personal websites.
Technology
yPredict: Innovative Predictive Tools for Advanced Traders

Introduction
In today’s fast-paced financial markets, having the edge can make all the difference between success and missed opportunities. Enter yPredict, a groundbreaking platform that merges artificial intelligence and machine learning to deliver sophisticated trading tools. Whether you’re an experienced trader or just starting out, yPredict’s innovative approach offers valuable insights and predictive capabilities that could transform your trading strategies. In this article, we will explore how yPredict stands out, its features, and how it can benefit advanced traders.
What is yPredict?
yPredict is a sophisticated trading research and analysis platform operating on the Polygon network. Designed for serious traders, it uses advanced algorithms to analyze vast amounts of financial data, providing users with predictive tools that can enhance their trading performance. The platform’s focus on AI and machine learning makes it a powerful tool for those looking to gain an edge in the competitive trading landscape.
The Technology Behind yPredict
At the core of yPredict’s innovation are its technological foundations. The platform employs a combination of AI and machine learning to process and analyze financial data. This technology allows for the creation of predictive models that offer actionable insights, helping traders to anticipate market movements and adjust their strategies accordingly.
Key Features of yPredict
1. Advanced Predictive Models: yPredict uses machine learning to develop sophisticated predictive models that can forecast market trends with high accuracy.
2. Real-Time Data Analysis: The platform provides real-time data analysis, enabling traders to make timely decisions based on the most current information.
3. User-Friendly Interface: Despite its advanced technology, yPredict offers an intuitive and easy-to-navigate interface, making it accessible for both novice and experienced traders.
4. Comprehensive Market Coverage: yPredict covers a wide range of financial markets, including stocks, cryptocurrencies, and forex, offering versatile tools for various trading needs.
How yPredict Enhances Trading Strategies
yPredict enhances trading strategies by providing actionable insights derived from its predictive models. Traders can use these insights to identify potential opportunities, minimize risks, and optimize their trading decisions. The platform’s ability to analyze large datasets and generate forecasts helps traders stay ahead of the curve and make data-driven decisions.
Benefits of Using yPredict for Advanced Traders
1. Increased Accuracy: Advanced predictive models improve the accuracy of market forecasts, leading to better trading decisions.
2. Time Efficiency: Real-time data analysis saves time by quickly processing large volumes of information and highlighting key insights.
3. Enhanced Decision-Making: Access to sophisticated tools and predictions helps traders make more informed and strategic decisions.
4. Versatility: yPredict’s broad market coverage allows traders to apply its tools across different financial markets.
Understanding the Polygon Network Integration
yPredict operates on the Polygon network, which is known for its scalability and low transaction costs. This integration ensures that users benefit from fast and efficient data processing, enhancing the overall performance of the platform. Polygon’s infrastructure supports yPredict’s sophisticated algorithms and provides a robust foundation for its predictive tools.
Artificial Intelligence in yPredict
AI is central to yPredict’s functionality. The platform uses AI to analyze historical and real-time data, identify patterns, and generate predictions. This technology enables yPredict to offer insights that are both accurate and actionable, helping traders navigate complex financial markets.
Machine Learning Algorithms
Machine learning algorithms are employed to refine predictive models continuously. By learning from past data and adjusting to new information, these algorithms improve the accuracy of predictions over time. yPredict’s use of machine learning ensures that its tools remain effective and relevant in a dynamic trading environment.
DAO Verification and Its Importance
One of yPredict’s unique features is its DAO (Decentralized Autonomous Organization) verification process. DAO members review and verify the platform’s trading models, ensuring their reliability and accuracy. This decentralized approach adds an extra layer of credibility to yPredict’s predictive tools and fosters trust within the trading community.
Comparing yPredict with Other Trading Platforms
When compared to other trading platforms, yPredict stands out for its advanced use of AI and machine learning. While many platforms offer basic analytics, yPredict’s predictive models and real-time data analysis provide a higher level of insight. Its integration with the Polygon network further distinguishes it by offering faster and more cost-effective transactions.
Real-Life Applications of yPredict
Traders have used yPredict to enhance their strategies across various markets. For instance, cryptocurrency traders utilize its predictive models to forecast price movements, while stock traders use real-time analysis to make timely investment decisions. The platform’s versatility and accuracy have made it a valuable tool for many in the trading community.
How to Get Started with yPredict
Getting started with yPredict is straightforward. Interested traders can sign up on the platform’s website, set up their accounts, and begin exploring its features. The user-friendly interface and comprehensive resources available on the platform make it easy to start leveraging yPredict’s advanced tools.
User Experiences and Testimonials
Many users have reported positive experiences with yPredict, highlighting its effectiveness in enhancing their trading strategies. Testimonials often praise the platform’s accuracy, ease of use, and the value it adds to their trading activities. These user experiences underscore yPredict’s reputation as a leading tool for advanced traders.
Conclusion
The 2024 GNU Gremlin is not just another snowboard; it represents a significant advancement in snowboarding technology. Its unique features, including the retro shape, mid flex, and C3 Aggressive All Terrain Contour, make it a standout choice for advanced riders. By integrating these features into a single board, the Gremlin delivers exceptional performance across various conditions, from powder to icy groomers. Whether you’re an experienced rider or looking to step up your game, the GNU Gremlin offers the tools you need to tackle the mountain with confidence and style.
FAQs
What makes yPredict different from other trading platforms?
yPredict differentiates itself with its advanced use of AI and machine learning, providing sophisticated predictive models and real-time data analysis that other platforms may not offer.
How does yPredict ensure the accuracy of its predictive models?
yPredict’s models are verified by DAO members, adding an extra layer of credibility and ensuring their reliability and accuracy.
Can yPredict be used for different types of trading?
Yes, yPredict covers various financial markets, including stocks, cryptocurrencies, and forex, making it a versatile tool for different trading needs.
What are the benefits of using AI in trading platforms like yPredict?
AI enhances trading platforms by providing accurate predictions, analyzing large datasets quickly, and offering actionable insights that improve trading strategies.
How do I get started with yPredict?
To get started with yPredict, sign up on the platform’s website, set up your account, and explore its features through the user-friendly interface and available resources.
-
 Shops1 year ago
Shops1 year agoPublix Pharmacy Hours and Locations
-

 Shops1 year ago
Shops1 year agoStaples Store Hours: What Time Does Staples Open And Close?
-

 Shops2 years ago
Shops2 years agoWalmart Vision Center Hours
-

 Shops1 year ago
Shops1 year agoWalgreen Pharmacy Hours: What Time Does It Open & Close?
-

 Business2 years ago
Business2 years agoDesigner Clothing: Making a Statement
-

 Entertainment2 years ago
Entertainment2 years agoRoku Red, White, and Blue: Streaming the cultural heart of America
-

 Shops1 year ago
Shops1 year agoWalmart Deli Open & Close Hours
-

 Shops2 years ago
Shops2 years agoKroger Deli Hours & Store Locations
